Beyond the Login
A unique platform for protecting data beyond the login
Most cybersecurity defenses focus on stopping hackers and fraudsters at the login page. We provide a second level of defense against the ones who break through.
Simple platform
Use advanced cyber defense with a simple user experience and one API
Cyphlens's unique platform and patented technology is designed to help banks, fintechs, and payment providers build and grow with confidence. From payment fraud to loan fraud, our world-class solutions are ready for rapid deployment.
Payments
Send wires after performing fully automated, secure electronic callbacks.
Cyber Risk
Use a more secure MFA and password reset tool that is MITM attack resilient.
Crypto
Secure seed phrases digitally and offer more secure crypto software wallets.
Unique cybersecurity protection
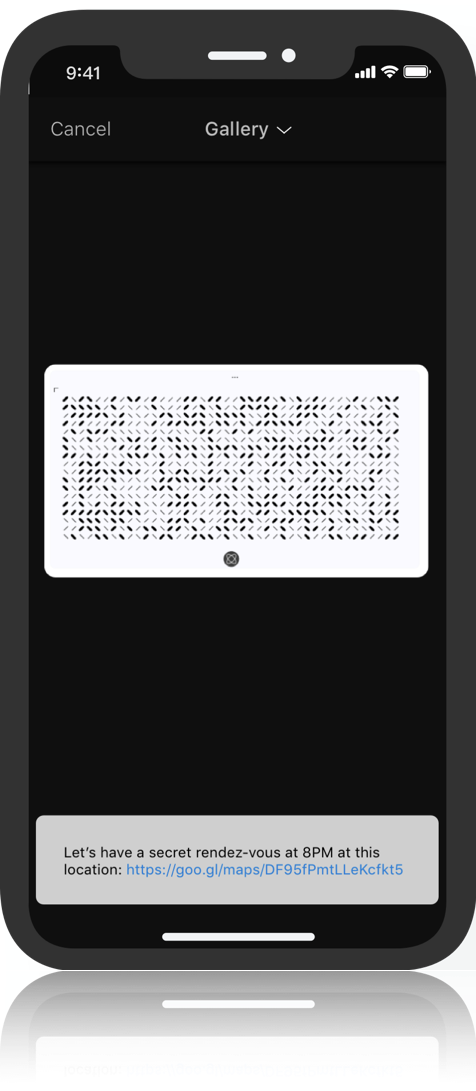
We fight fraud by protecting transactions after the login
With Cyphlens, accessing, viewing and sharing transactional data is secure and resilient against advanced targeted attacks and malware.
Man-in-the-middle attacks
Provide an extra layer of defense for sensitive transactional data during an attack.
Data-in-view decryption
Add the protection of an encryption layer to content viewing in real time.
Account compromise
Stop hackers from accessing critical information after an account is compromised.